Archamps - 15 May 201
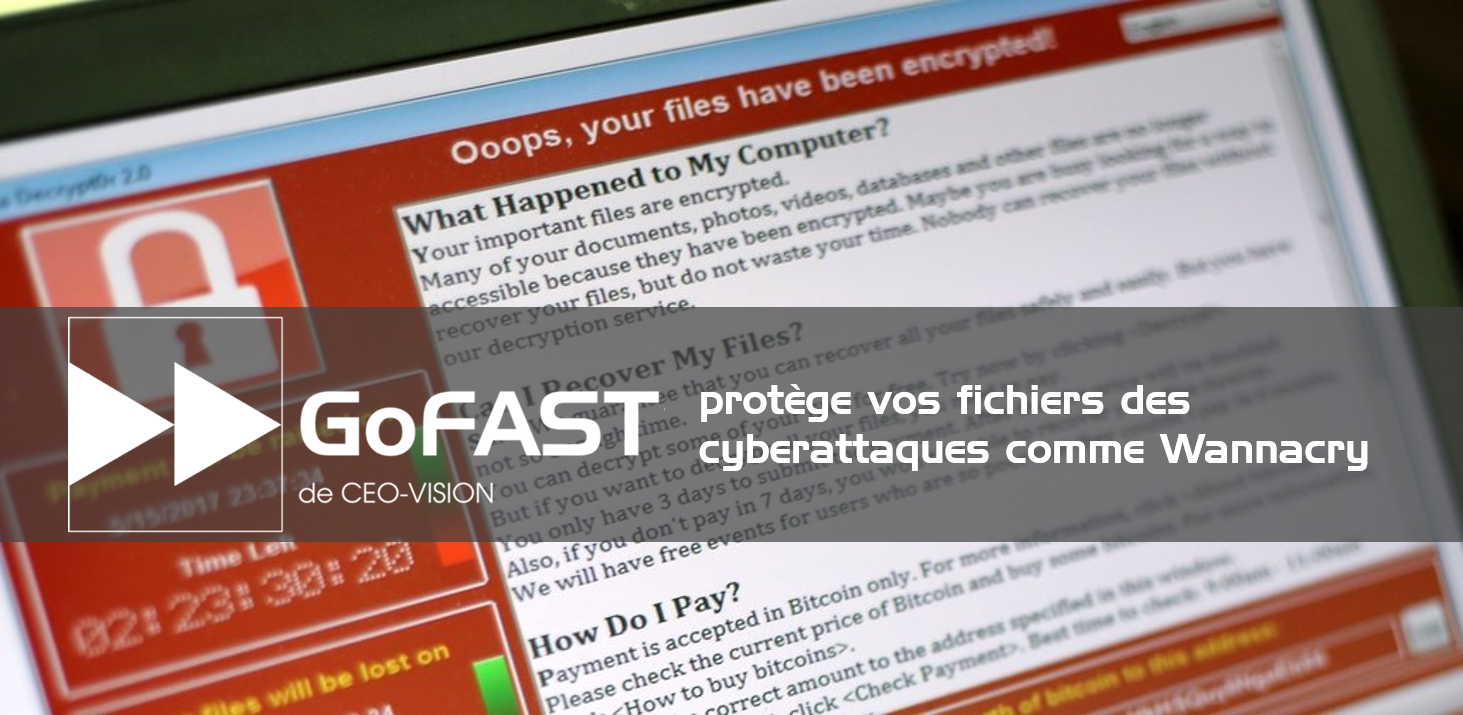
The Collaborative platform and DMS GoFAST secures your files against cyber attacks like Wannacry and allow you to recover lost data.
There were at least 200,000 victims in almost 150 countries suffered from a massive cyber attack launched on last May 12. This attack made the documents inaccessible by encrypting them and demanding a ransom in exchange for the restoration.
Avoid blackmail with GoFAST solution :
-
GoFAST automatically keeps all modifications of your files by saving each time a new version, including when there is an attack by "Wannacry".
-
At the time of encryption, GoFAST creates a new version of the affected files
-
Then it becomes possible to restore the versions into their state before the attack and avoid blackmail.
Microsoft Software is targeted by hacking:
In general, this type of attacks is triggered by opening of specific emails or attachments. In this case, the "Wannacry" virus, which encrypts the files, exploits the vulnerabilities which were initially used by the NSA as cyber-weapons (Eternalblue) and then "lost in the wild".
As a counter-measure of these cyber attacks, Microsoft had to reactivate a security update of its software, some of which have not been supported for years (ex: Windows XP). Many companies and administrations that still use these old versions, or those who have their not updated recent version, are among the most vulnerable.
GoFAST technology will help you to avoid cyber attacks :
GoFAST has the advantage of running on VMs under CentOS (using Webdav), open source technology not targeted by the cyberattack "Wannacry" (using Microsoft SMB v1 protocol). Microsoft's solutions are among the most affected by this type of attack, that is why the choice of GoFAST significantly reduces the risk of being targeted.
Other best practices :
-
Have an updated anti-virus
-
Train employees in good practice, such as knowledge how to distinguish a fraudulent email or scanning suspicious attachments with an antivirus.
-
Update applications with security patches as soon as they are available.
-
Set up a backup/restore solution of the company's servers or public administration, independent of the internal IS network.